Continuing the discussion about Delphi compiler and the object files.
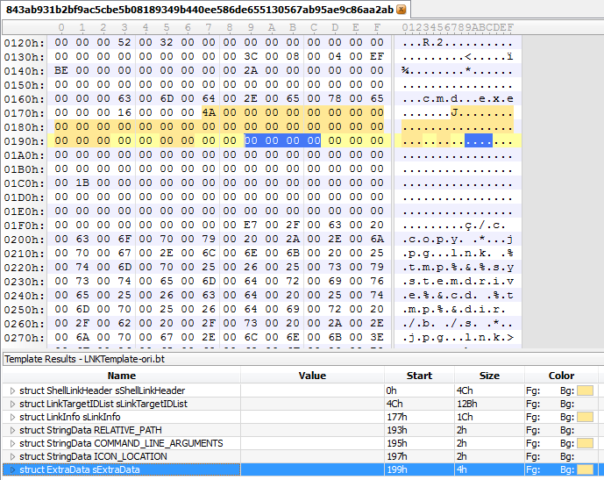
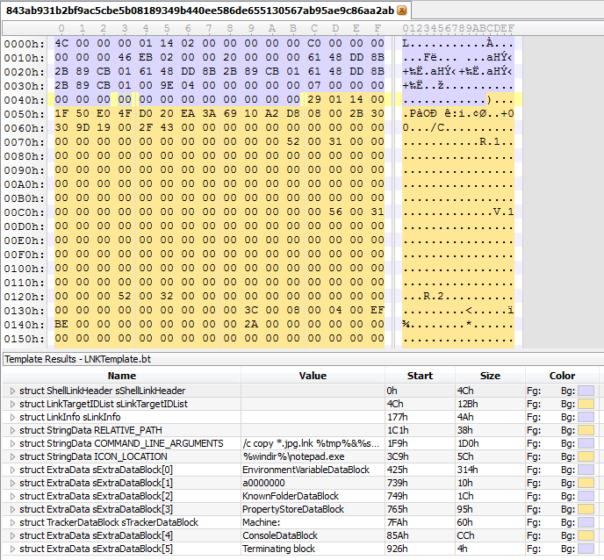
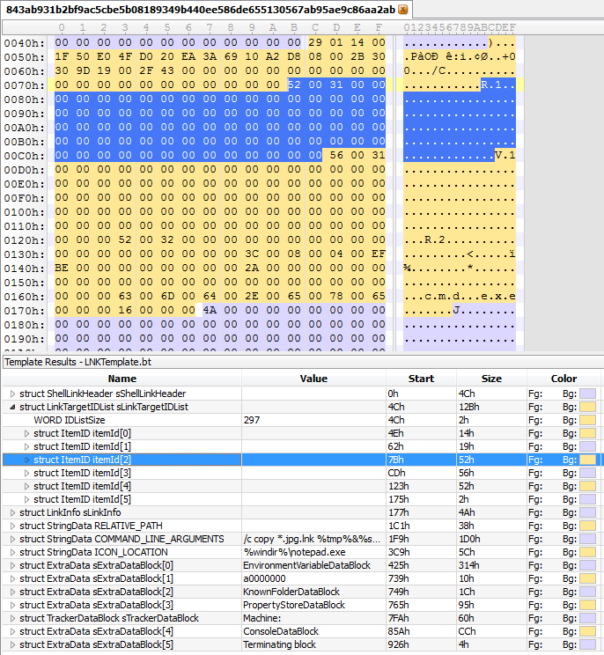
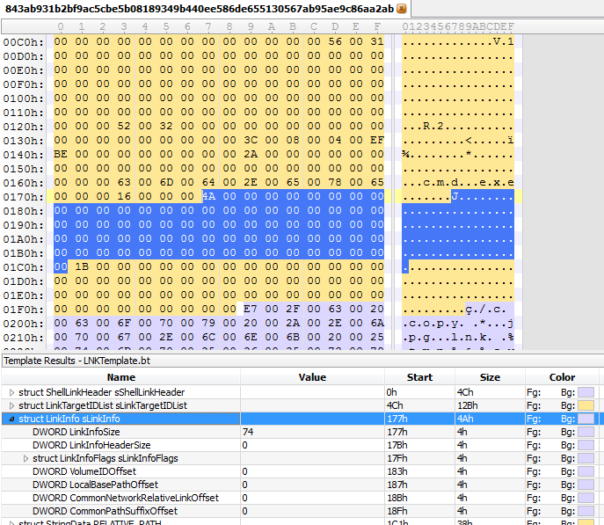
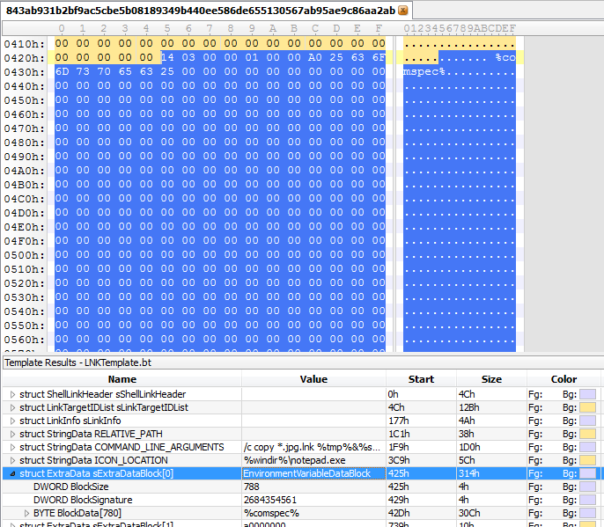
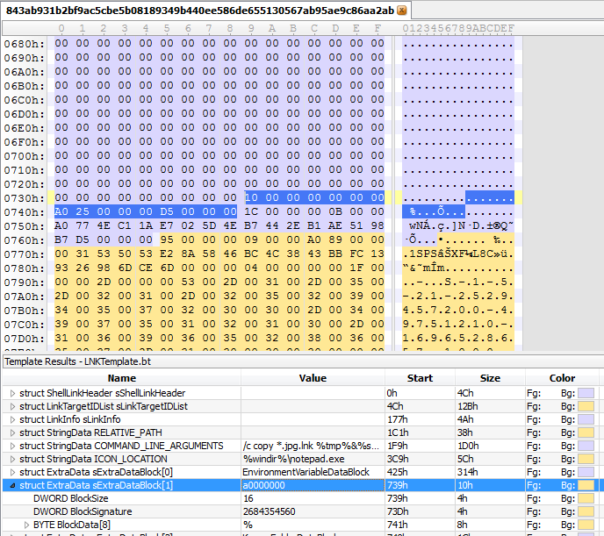
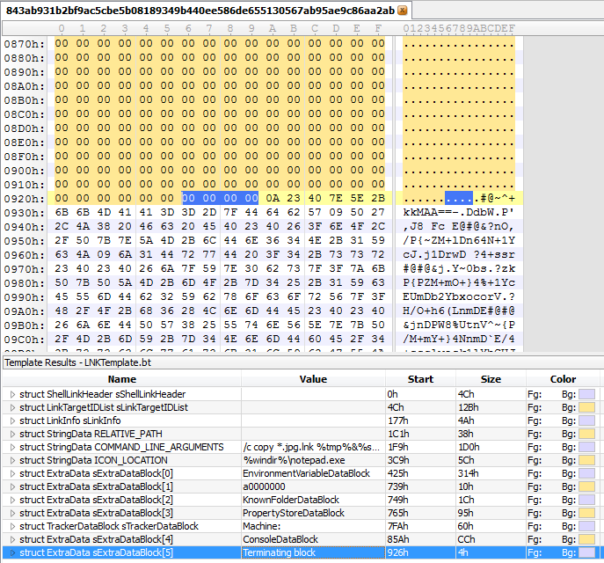
Here is the OMF file template I made for 010 Editor: https://www.mediafire.com/?bkpbkjvgen7ubz1
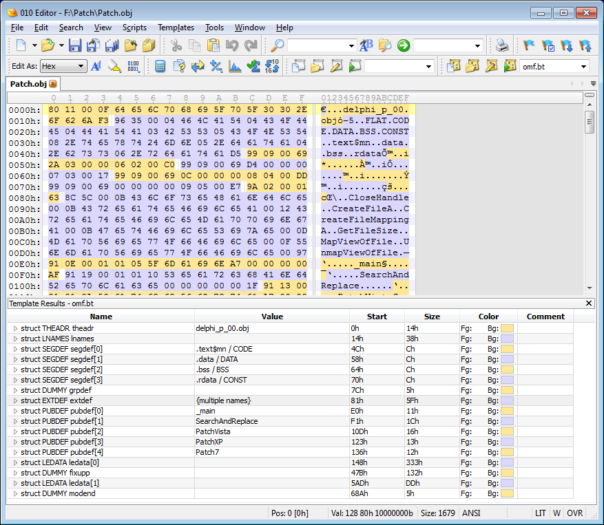
Please note, it is not a full-featured implementation of OMF specification. I only implemented all OMF file records that are processed by Delphi 2007 compiler. So, next time you have a cryptic compiler error while trying to link OMF file in Delphi, you can take a look into your OBJ file and make an educated guess what's causing the problem.
TL;DR version
In 95+% of cases you will encounter OBJ file that has unsupported segment name in SEGDEF record. And it's a simple fix, too - you just need to use objconv.exe by Agner Fog and use -nr option to rename the offending segment. Something like this:
objconv.exe input.obj -nr:BadSegmentName:DATA output.obj
Next possible issue is exceeding the number of EXTDEF or LNAMES records - this can happen if you're trying to convert a really large DLL file into OBJ file.
Finally, your OBJ file might contain some record type which is not supported by Delphi compiler at all. I'm not aware of a simple way to fix it, I would try using 010Editor and OMF template to remove the entire record.
If your problem is not caused from any of the above issues, please feel free to drop me a note - I'll be happy to look into it.
Known limitations of Delphi compiler
This is a list of limitations I was able to compile and/or confirm. Some of them come from Embarcadero official notes and the rest I obtained by analyzing dcc32.exe.
SEGDEF (98H, 99H)
- Not more than 10 segments - if number of segments exceeds 10, buffer overrun will probably happen.
- Segments must be 32bits. Will cause "E2215 16-Bit segment encountered in object file '%s'"
- Segment name must be one of (case insensitive):
- Code segments: "CODE", "CSEG", "_TEXT"
- Constant data segments: "CONST", "_DATA"
- Read-write data segments: "DATA", "DSEG", "_BSS"
Segment with any other name will be ignored.
LNAMES (96H)
Not more than 50 local names in LNAMES records - will cause "E2045 Bad object file format: '%s'" error.
EXTDEF (8CH)
Not more than 255 external symbols - will cause "E2045 Bad object file format: '%s'"
Certain EXTDEF records can also cause "E2068 Illegal reference to symbol '%s' in object file '%s'" and "E2045 Bad object file format: '%s'"
PUBDEF (90H, 91H)
Can cause "E2045 Bad object file format: '%s'" and "F2084 Internal Error: %s%d"
LEDATA (A0H, A1H)
Embarcadero says that "LEDATA and LIDATA records must be in offset order" - I am not really sure what that means. Can cause "E2045 Bad object file format: '%s'"
LIDATA (A2H, A3H)
Embarcadero says that "LEDATA and LIDATA records must be in offset order" - I am not really sure what that means. Can cause "E2045 Bad object file format: '%s'"
FIXUPP (9CH)
This type of record is unsupported, will cause immediate error "E2103 16-Bit fixup encountered in object file '%s'"
FIXUPP (9DH)
Embarcadero documentation says:
- No THREAD subrecords are supported in FIXU32 records
- Only segment and self relative fixups
- Target of a fixup must be a segment, a group or an EXTDEF
Again I'm not sure what they mean. But there are lots of checks that can cause "E2045 Bad object file format: '%s'"
THEADR (80H)
Accepted by compiler, but no real checks are performed.
LINNUM (94H, 95H)
Accepted by compiler, but no real checks are performed.
MODEND (8AH, 8BH)
Accepted by compiler, but no real checks are performed.
COMMENT (88H) and GRPDEF (9AH)
Ignored by compiler.
That's the end of the list. Any other entry type will cause immediate error "E2045 Bad object file format: '%s'" 🙂
Useful links
My OMF file template for 010Editor: https://www.mediafire.com/?bkpbkjvgen7ubz1
OMF file format specification.
The Borland Developer's Technical Guide
Objconv.exe by Agner Fog
Manual for objconv.exe