For last few years I'm taking part in the FLARE-ON competition. This year I finished 4th - which is not bad at all. 🙂
Now that the challenge is over, it's fun to read all the solutions. Of course, there are official solutions - they explain what the challenge does and one way how to solve it. Nice but I want more. 🙂
Then there are "writeups" which basically say "this is my code that gets the answer". Dude, if that makes your e-penis seem bigger, feel free to twit about it. But I don't care about your code. Really.
What I do care about, is how the challenge can be solved. So, here are few selected challenges and related writeups that actually make sense.
Challenge #2 - minesweeper
I wasted too much time on it, relatively speaking. Whopping 37 minutes, on a challenge #2!
I will blame the fact that I was barely awake at the time. In the end I resorted to editing variables in dnSpy, just like @bruce30262 does in his solution.
Other solutions:
* By @mathmare_ - remove IL that triggers failure.
* By @jared703 - find the correct spots.
* By @Eleemosynator - another "find the correct spots".
* By @bruce30262 - edit variables in dnSpy.
Challenge #5 - webassembly
It was my first real encounter with Webassembly, so I just used Chrome to debug it. Plus wabt just to get a better look at the disassembly. It wasn't that bad in this particular case.
Since I don't really do Linux and gcc, I wasn't able and willing to try WASM-to-C conversion and compilation to x86 code. 😀
Other solutions:
* By @ctfhacker #1 - uses Chrome, shows the recompilation as well.
* By @ctfhacker #2 - uses wasabi.
Challenge #6 - solving 666 tasks on Linux
My Linux skills suck and I wasn't able to find a reliable way to pipe output from my solver into the challenge.
So I solved the task like a trained monkey.
![]()
This bash crap uses gdb to get current challenge from process memory and feeds it to my C# solver running under Mono. Output from solver gets fed to xclip which puts solution into the clipboard. Then I right-click mouse and paste solution into the challenge window. Repeat 666 times. The entire process takes around 20-30 minutes. Click-click-click-click..
Yes, it's extremely inefficient and braindead stupid - but the result is guaranteed and faster than spending hours trying to learn how to automate Linux tools.
Other solutions:
* By @MrAdz350 - uses Unicorn, pexpect.
* By @crudd40233929 - patches original binary to generate keys, uses pexpect.
* By @0xabc0 - uses Frida.
* By @bruce30262 - uses pwntools to send answers to challenge.
* By @ctfhacker - shows how to use angr. Solver needed 28 hours to finish! 😀
Challenge #12 - VM inside the VM
This challenge actually consisted of 2 separate parts - 16-bit bootkit and a nasty VM in the VM. Since it was the final challenge, everyone just focused on breaking the VMs. It's a shame because the bootkit part was extremely nice and deserved much more attention than it actually received.
Until the official solutions came out, I didn't know that Subleq code actually ran another VM! Why? Because my solution was data-flow analysis done with pen and paper. When I finished, it looked like this:
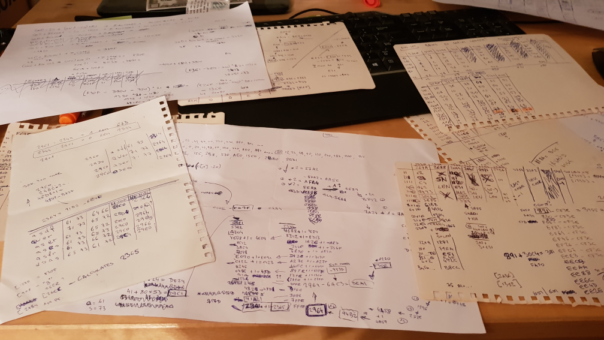
Yes, all 10 pages are from this challenge.
Close-up of one of the pages:
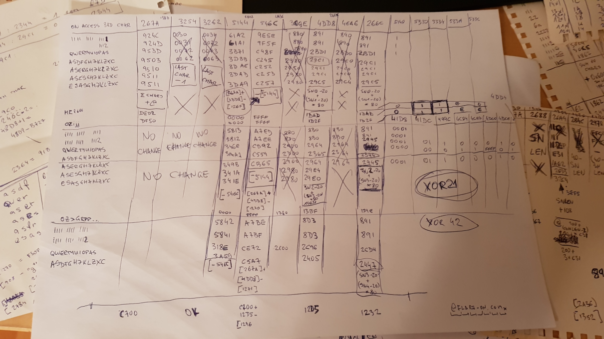
Each row contains a flag that I traced, columns are the "cell indexes" of Subleq VM and values are the values I observed during the run. Plus notes, plus attempts to recover the formula..
Kids, don't try this at home! 🙂
Other solutions:
* By @bruce30262 - writing 2 disassemblers.
* By @SalimSolid - tracing instruction pointer.
* By @invano #1 - cat'n'grep
* By @invano #2 - disasm + recognize high-level macros.
* By @Dark_Puzzle - snapshotting VMs and bruteforcing chars.
Hi Kao,
Thanks for providing other solutions as well.
Method for solving level#6, lol.
For me. I solved level#2 by changing single piece of code in onpaint method of GUI. 🙂
Still wait to see your solver for last year VM challenge #11.
Thanks
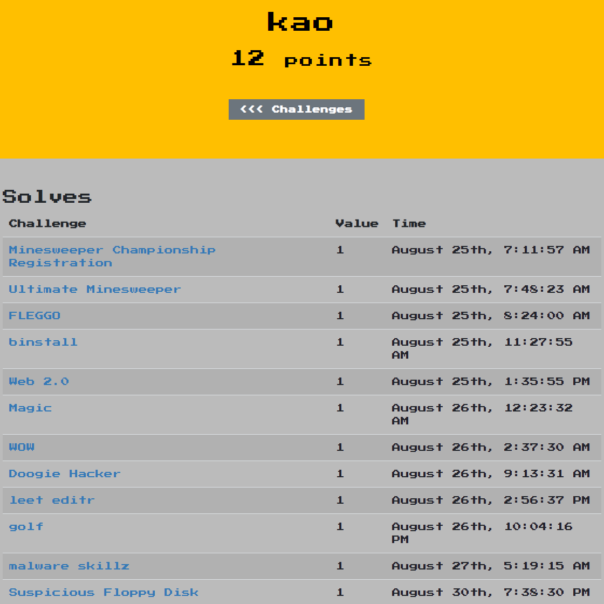
Did you even sleep between the 25th and 26th of August? Haha, besides that congrats kao!
Thanks! 🙂
It is a very nice question and I wanted to write about sleeping in a follow up post about FLARE and CTF challenges in general. But since you asked - yes, I did have some sleep after solving WOW.
You can stay up all night and feel quite ok - but your actual brain performance suffers a lot.
Ref. https://www.bustle.com/articles/140910-what-happens-to-your-body-when-you-dont-sleep
Interesting, thanks for your reply! Excited to read the upcoming blog post.
Can you post your c# solver of magic? It's quite interesting 🙂
Sure, here it is: https://gist.github.com/kao-was-here/939db256d91cb74c8f5cdab67b53e3ad See the bash command in blog post for usage.
Please keep in mind, this is the original file as written during competition. There is no error handling, no comments, lots of unused code and so on. It's not something to be used for learning. 😉
If I get some free time, I'll add the polished version as well. But that's a very big "IF"...