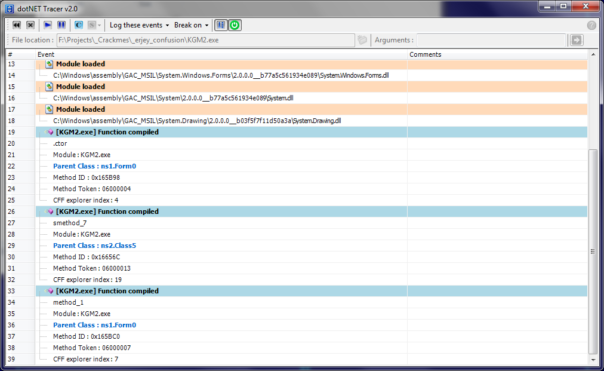
dotNET Tracer is a great tool created by my friend Kurapica. It provides information really useful for analyzing different .NET protections, like which modules are being loaded, which functions are being JIT-compiled, and so on.
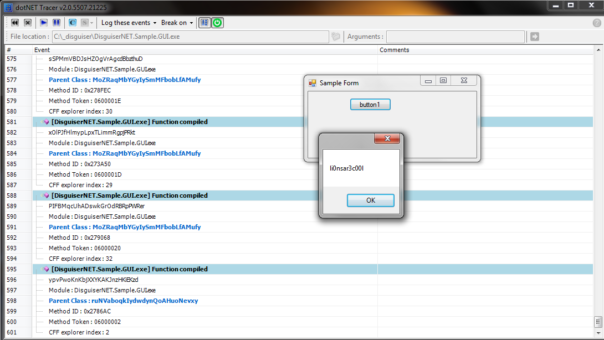
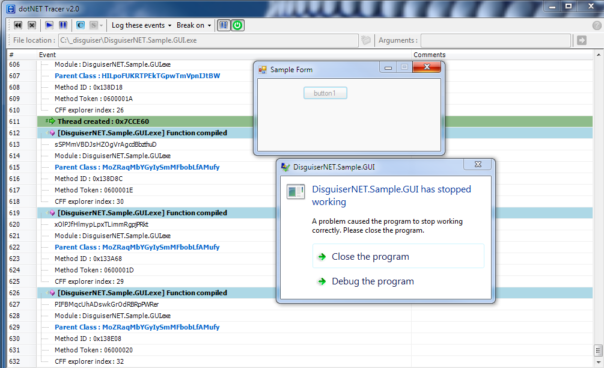
Unfortunately, it is missing some features and has some small bugs. For example, DisguiserNET.Sample.GUI unpackme by li0nsar3c00l (another friend of mine!) detects dotNET tracer and refuses to run:
Cause of the problem
It's actually quite simple. dotNET Tracer is using .NET CLR Profiling APIs to gather the information. To do that, it needs to set several environment variables, as you can see in the Form_Main.cs:
ProcessStartInfo ProcessSInfo = new ProcessStartInfo(this.toolStripTextBox_FileName.Text, this.toolStripTextBox_args.Text);
ProcessSInfo.EnvironmentVariables.Add("COR_ENABLE_PROFILING", "1");
ProcessSInfo.EnvironmentVariables.Add("COR_PROFILER", "{7A460847-6B67-4C0C-883E-21B233A6DEF8}");
ProcessSInfo.EnvironmentVariables.Add("COMPLUS_ProfAPI_ProfilerCompatibilitySetting", "EnableV2Profiler");
After profiling dll (system.dll) is initialized, it resets first 2 environment variables, but forgot to reset the 3rd one. Disguiser detects presence of that variable and crashes. Oops.
Solution
After spending some time on both tracer and the unpackme, I'm happy to present a fixed version of dotNET Tracer. So far I have improved:
- Created workaround for li0n's anti-profiler trick;
- Added logging of "Module load finished" events. This prints imagebase for loaded DLLs and thus makes dumping resources from memory easier;
- When you close dotNET Tracer, traced process will be killed automatically.
Now I can spend more time on the unpackme.. 🙂
Download link for binaries: http://www.mediafire.com/?8zfaukefx39i32n
I respect Kurapica's wishes and therefore source code will not be made available.
Nice work 🙂
hi kao i'm using this improved version , but still got this problem you said above when i load Crypto Obfucation app to it
@keosoft90: Kurapica released an updated version of dotNET Tracer at Black Storm forum (http://board.b-at-s.info/index.php?showtopic=8010#entry23341), please try that one. If it still doesn't work, leave a comment with a download link for your executable+all necessary files and I'll see if it can be fixed.
Made some updates
* Added commandline support
* improved right-click-jumps to .net Reflector
{hidden link}
_________________________________________________________________________
btw incase you like to sign up at the Black Storm forum that python line might
[ chr(int (x, 16) ) for x in "68 65 6C 70".split() ]
you to asker their registration question. 🙂
"".join( [ chr(int (x, 2) ) for x in "0b1001000 0b1100101 0b1101100 0b1101100 0b1101111 0b100000 0b1010111 0b1101111 0b1110010 0b1101100 0b1100100 0b100001".split() ] )
Comment approved, even though I generally don't allow other people to do self-promotions on my blog. 😉
Disclaimer: I haven't checked the link above. Use at your own risk.
Just in case anyone wants to look at cw2k's version: http://bit.do/KDT_2_1
Link got hidden when I changed the system for moderating comments, sorry about that.
Does not work on Windows 64-bit software
can you give us the updated version of tracer? i cant seems to register to blackstorm due to questions indicated to them. also can i request to register me in blackstorm? thanks
My version is still available, download link is in the end of the post. If you want Kurapica's version, just google for some public links. There are lots of them..
Please remember that this blog post was written in year 2015, there might be a better tools now.
Thank you again admin Kao.Your so good . Can you please accept me as your friend in gmail or any chatting app so i can talk and send you message .
Please also publish for 64-bit Windows software