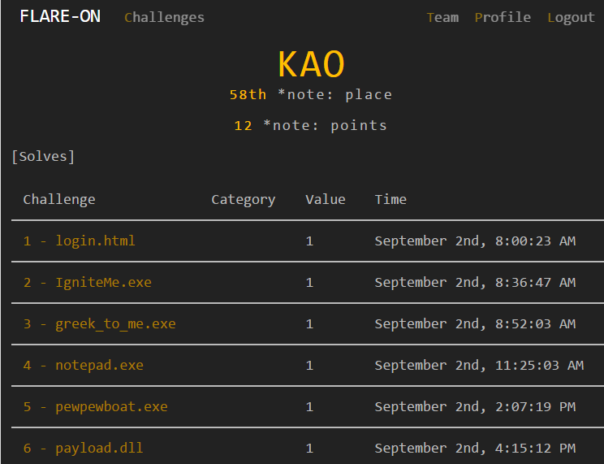
This was the 3rd time I played Flare-On reverse-engineering contest. And I must say, this year was much nicer than the last. Challenges were more balanced, didn't require insane arcane knowledge and rick-rolling was kept to a reasonable minimum.
As for me - I wasted too much time and effort in challenge #7 and stopped competing at that point. Later I spent few hours every weekend just to finish the entire contest on time.
I'm not planning make full-featured writeups, so here's just an overview of this year's challenges.
#1 - login.html
ROT13, what else?
Time spent: 20 seconds
#2 - IgniteMe.exe
It's XOR. For some reason I kept messing up my answer. I guess I wasn't really awake yet. 😀
Time spent: 30 minutes
#3 - greek_to_me.exe
Bruteforce the correct byte value which will decode valid x86 code which will get you the flag. Simples.
Time spent: 15 minutes
#4 - notepad.exe
The worst challenge in the contest. To decrypt the flag, one must get data from last years challenge files. Self-centered ego masturbation, anyone?
Time spent: 2.5 hours
#5 - pewpewboat.exe
Linux challenge in form of a Battleship game with hardcoded levels. Simple to patch to reveal all ships and equally simple to write a C# decryptor that will decrypt all levels.
Time spent: 2.5 hours
#6 - payload.dll
You get a DLL and then mess with it's exports. Reminded me very much of last year's challenge #4.
Time spent: 2 hours
#7 - zsud.exe
It's a single-player dungeon. You get a native executable that functions also as .NET CLR host and as a web server. It loads a .NET DLL which in turn decrypts PowerShell code. PowerShell code then functions as a web client, sends the player's moves to server, server validates it and sends the result back.
I followed the wrong path and got stuck. I got to the powershell code all too quickly and neglected to look at the process itself. If I had done that, I would have noticed hooked API functions and would not have wasted too much time trying to bruteforce my way through..
Time spent: way too much
#8 - flair.apk
Mandatory Android challenge. It looked like there could be some anti-debug checks but JEB worked just fine. I solved each stage be reimplementing the check in C# and then breaking it.
Time spent: few hours
#9 - remorse.ino.hex
Arduino challenge, that's a first! 🙂 I had to learn AVR assembly, find out how to debug stuff in Atmel Studio 7 and it was a walk in the park from there.
Note to self - IDA's support for Atmega is crap. Atmel Studio kicks ass.
Time spent: few hours
#10 - shell.php
PHP challenge. Boring. It all boils down to obtaining the correct XOR key by making intelligent guesses on how the valid PHP code looks like. Repeat 4 times for extra boredom.
Time spent: few hours
#11 - covfefe.exe
It's a VM. It has one instruction. It self-modifies the code. Very nice! 😀 I solved it by making dynamic disassembler/emulator in C#. Just after solving it, I learned about OISC and subleq in particular..
Time spent: 6-8 hours in total?
#12 - [missing]
This was probably my favorite CTF challenge ever. You get a PCAP and a malware binary. You must decode custom protocol malware uses to communicate with the bad guys and extract all the data from packets. Throw in some dynamic plugins for encryption, compression and commands and you get a whole lot of fun stuff to analyze. Awesome! 😀
Time spent: ~18 hours in total?