CFF Explorer is another invaluable tool for .NET reversers. Unfortunately it is closed-source and is not actively maintained anymore.
One of the most annoying problems is that it cannot correctly process .NET metadata in some assemblies protected by ConfuserEx (and few other protectors).
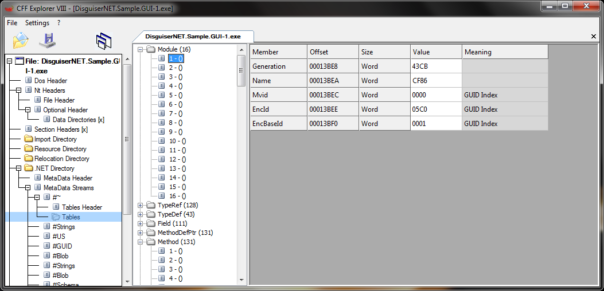
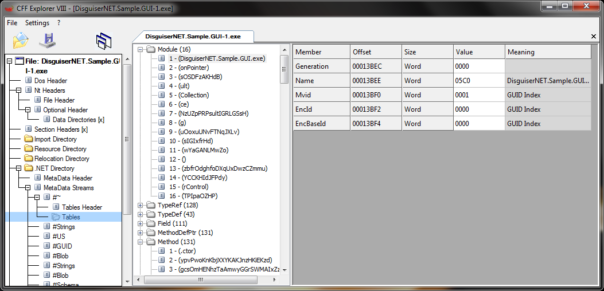
As you can see, Module data make no sense and Methods also look weird.
Cause of the problem
The problem is caused by obscure and undocumented field in Metadata Table Stream. DNLib is one of the very few tools/libraries that properly supports it:
////// MDStream flags /// [Flags] public enum MDStreamFlags : byte { ///#Strings stream is big and requires 4 byte offsets BigStrings = 1, ///#GUID stream is big and requires 4 byte offsets BigGUID = 2, ///#Blob stream is big and requires 4 byte offsets BigBlob = 4, ///Padding = 8, /// DeltaOnly = 0x20, /// Extra data follows the row counts ExtraData = 0x40, ///Set if certain tables can contain deleted rows. The name column (if present) is set to "_Deleted" HasDelete = 0x80, } ... ////// Gets the public bool HasExtraData { get { return (flags & MDStreamFlags.ExtraData) != 0; } } ... ulong valid = validMask; var sizes = new uint[64]; for (int i = 0; i < 64; valid >>= 1, i++) { uint rows = (valid & 1) == 0 ? 0 : imageStream.ReadUInt32(); if (i >= maxPresentTables) rows = 0; sizes = rows; if (i < mdTables.Length) mdTables[i] = new MDTable((Table)i, rows, tableInfos[i]); } if (HasExtraData) extraData = imageStream.ReadUInt32();bit ///
This extraData field is causing us troubles.. Oh, well, it's time to fix it! 🙂
Solution
Since CFF Explorer is closed-source, I had to reverse-engineer parts of it. Then I created a small code cave and added extra code that checks flag value and skips over extraData field, if necessary. If you're interested how exactly it was done, check address 004689CC and added code at 00589800.
Download link for patched EXE: Please get latest version from this post