My last posts about Unity3D/Mono protections gained a lot of attention. Unfortunately, they gained the wrong kind of attention and low quality comments. So, I decided to make changes in a way these posts are made.
This is a place to describe HOW the protection works.
I have no agenda against game authors or any of the Android MOD teams. They just happen to use interesting protection mechanisms. And I like to take protections apart and describe HOW they work. So, the posts will be even more focused on HOW the protection works and how it can be defeated. Sometimes I'll make some code snippets available. But in any case, you will have to do your work to defeat the protection.
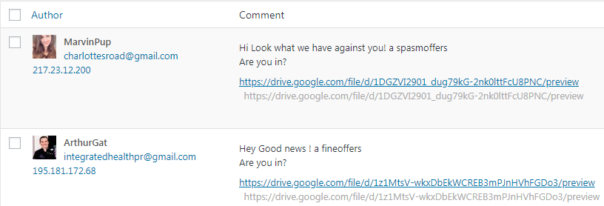
This is NOT a place for script-kiddies.
I made a big mistake releasing compiled executable. It attracts crowds of asian kids who are only able to drop DLL on the compiled executable and complain that it did not magically fix everything. They have absolutely no interest in how the protection actually works.
To fix that, there will be no more ready-made tools. If you care about the protection, my blog has all the information you need to make your own tool. But if you need a ready-made, compiled tool, go somewhere else.
This is NOT a place for crack requests.
Yes, I'm always interested in new and innovative protections. If you tell me about such protection, I will be very happy. When I get some free time, I will look at it. If it's interesting enough, I will write about it.
But I will not crack the protection for you. And most certainly I will not do it on your schedule. So, don't bug me about that.
I work on this blog in my free time.
My free time is limited. I will read all comments and all emails. Someday. When I have free time.
So, do NOT bump your comments or your emails. If you haven't received a reply, your message was stupid and I decided to ignore it. Or perhaps I just haven't had time to read it and respond to it.
You need to do your homework.
I got plenty of comments like "how do I use your tool?" or "I can't open file in dnSpy. Help!!!111".
First, read the bloody posts, they explain how my tools work and what the limitations are. Second, use Google. Third, read "How to Report Bugs Effectively". I can't magically solve all your problems - I need to see the actual file first.
I hate using ban-hammer. So, first time you do something stupid, I will warn you. But if you continue doing that, I'll ban you. As simple as that.
Thank you for reading to the end, I really appreciate that. Please enjoy your stay here.